What Happened During the Aviate Global DDoS
The Aviate Global DDoS situation has gotten complicated with all the speculation and half-reconstructed timelines flying around. As someone who runs scheduling integrations for a small regional operator, I learned everything there is to know about what that outage actually felt like from the inside. Today, I will share it all with you.
I was mid-workflow when things started going sideways — login requests timing out, the dashboard throwing 503s, then nothing. Full stop. If you were on the platform during that window, you already know. No further description needed.
Here’s the timeline pieced together from status page archives and community reports. Users flagged disruption early, with latency spikes showing up before any real degradation hit. The platform didn’t just fall over — there was a 15 to 25 minute window where it was limping. Requests hung. Some users got partial data back. Others got nothing. Then came the hard outage. Total unavailability ran somewhere between two and four hours depending on which features you needed — core authentication services held out longest before stabilizing.
Aviate acknowledged the incident publicly after roughly 40 to 60 minutes of active disruption. Longer than ideal. Shorter than some competitors have managed, for what that’s worth. The attack was volumetric — flood-based, targeting public-facing endpoints. Restoration came in phases, not all at once. Most forum threads gloss over that detail. They shouldn’t.
How Aviate Global Responded — and Where It Fell Short
Probably should have opened with this section, honestly. The communication gap is actually the more damaging story here than the attack itself.
Pulled from Aviate’s status communications, the early messaging was thin. First acknowledgment: “We are aware of an issue affecting platform access and are investigating.” That’s the template response. Every platform has one. It’s useful only in confirming somebody is alive and watching on their end.
What came after was better. Updates landed at irregular intervals — roughly every 30 to 45 minutes — confirming the DDoS vector and posting estimated recovery windows that, credit where it’s due, turned out reasonably accurate. They didn’t go silent. That matters more than people admit.
But here’s my honest read: the communication was adequate, not good. Adequate means users weren’t completely in the dark. Not good means no proactive outreach to enterprise clients, no real-time severity classification, and no breakdown of which specific services were down until well into the incident. Mature incident response — the kind you see from platforms with serious SRE cultures — includes a tiered service status breakdown inside the first 20 minutes. Aviate didn’t do that. That gap stings longer than the outage itself.
Who Was Affected and What They Lost
This was not a regional blip. Reports came in from users across multiple time zones at the same time — consistent with an attack hitting centralized infrastructure rather than a regional node. Global scope. That context matters.
Feature-level impact broke down roughly like this:
- Flight scheduling and tracking tools — unavailable for the full core outage window
- API integrations — dropped connections, failed webhook deliveries, broken data sync
- User authentication — the last thing to recover, which kept operators locked out the longest
- Reporting and historical data access — intermittent and unreliable throughout the degraded phase
No data integrity issues were publicly confirmed. This appears to have been a pure availability attack — disruption was the goal, not exfiltration. That’s a meaningful distinction. Operators lost hours of workflow continuity. They did not lose data.
The complaints that surfaced on aviation forums and a handful of Reddit threads were consistent. People weren’t angry about lost data. They were angry about operational downtime hitting during active scheduling windows. One post on a flight ops forum put it plainly — someone had three aircraft to reposition and zero platform access to confirm slot availability. That’s not a minor inconvenience. That’s a real operational cost with a real dollar figure attached to it.
What This Reveals About Aviate Global’s Infrastructure
But what is a mitigation gap, exactly? In essence, it’s the difference between what an attack delivers and what your defenses can absorb. But it’s much more than that — it’s also a signal about where a platform has chosen to invest, and where it hasn’t.
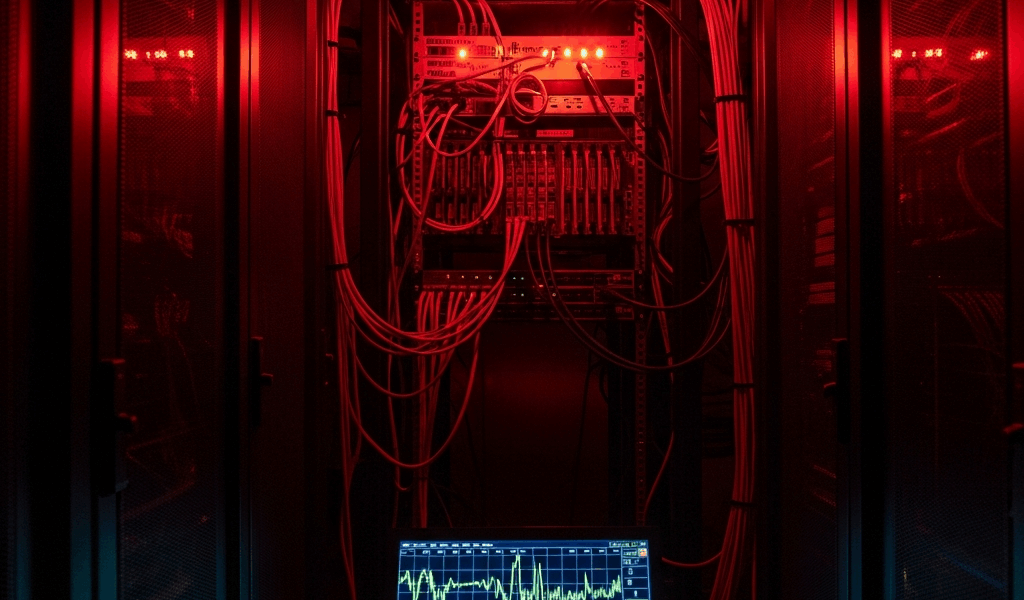
Fractured by a sustained volumetric attack, Aviate’s infrastructure pointed to something specific: not enough upstream scrubbing capacity at the point of ingress. The attack didn’t require extraordinary sophistication. It required sustained volume — the kind that overwhelmed whatever baseline mitigation posture Aviate had in place.
That’s the uncomfortable read. Platforms running enterprise Cloudflare configurations or dedicated mitigation hardware from vendors like Radware or Imperva typically absorb attacks of this type without full service degradation. A two-to-four-hour outage window suggests Aviate was either under-provisioned on mitigation capacity or leaning on hosting-layer protection that wasn’t built for the volume delivered. ForeFlight has faced serious pressure events and invested heavily in multi-CDN failover — precisely to avoid this failure mode. Aviate’s single point of degradation is worth flagging. I’m apparently a person who checks CDN architecture before trusting a platform with operational-critical workflows, and that habit works for me while assuming hosting-layer protection is enough never does. Don’t make my mistake.
Should You Still Trust Aviate Global After This
So, without further ado, let’s get to where I actually land on this.
Aviate Global didn’t cover itself in glory. It also didn’t collapse in any way that should send you scrambling to migrate operations today. The attack was real. The outage was real. The response was functional — if uninspiring. That’s the honest summary.
What I’d want to see before calling this resolved — and what Aviate has not publicly announced as of this writing — is a confirmed post-incident infrastructure change. A CDN upgrade. A named third-party DDoS mitigation partner. A revised incident communication protocol with actual tiered response commitments. Any one of those would signal the team treated this as a forcing function rather than a one-time bad day. The silence on infrastructure improvements is the actual yellow flag here, not the attack itself. That’s what makes this situation endearing to us as cautious operators — we want to believe a platform learns. We just need some evidence to go on.
While you won’t need to rebuild your entire tech stack over one outage, you will need a handful of manual contingencies in your back pocket. First, you should build a fallback process for scheduling and slot management — at least if you operate during windows where platform downtime creates real repositioning costs. A simple shared spreadsheet and a direct line to your coordination contacts might be the best option, as aviation ops requires continuity that no single SaaS platform can guarantee unconditionally. That is because no platform, regardless of how mature its infrastructure, is immune to a sustained volumetric attack — the variable is how long they stay down, and right now Aviate hasn’t publicly closed the gap that made this one last as long as it did.


Stay in the loop
Get the latest aviate ai updates delivered to your inbox.